What Is TTL in Networking?
TTL stands for Time to Live. It is a value embedded inside every IP packet that controls how many network devices — specifically routers — that packet is allowed to pass through before it is discarded. Despite the name suggesting a time-based limit, TTL in networking actually functions as a hop counter. Each time a packet crosses a router, the router subtracts one from the TTL value. If the TTL reaches zero before the packet arrives at its destination, the router that decremented it to zero drops the packet entirely and sends an error message back to the sender.
Every device that sends data over an IP network sets a TTL value in the packet header before transmission. This value occupies an 8-bit field in the IPv4 header, which means it can range from 0 to 255. In practice, most operating systems set a default starting TTL of 64, 128, or 255 depending on the platform. The TTL field exists in every single IP packet — whether it carries a web request, a DNS lookup, a ping, or a file transfer. It is not optional. Without it, a misdirected or misrouted packet could circle through the internet indefinitely, consuming bandwidth and router resources with no purpose.
Understanding what TTL means in networking is foundational for reading ping output, diagnosing routing issues, interpreting traceroute results, and even fingerprinting remote operating systems. It is one of the first values network engineers look at when troubleshooting connectivity problems.

Why Was TTL Invented — The Routing Loop Problem
Routers forward packets based on routing tables — lists that tell each router where to send traffic destined for a particular network. These tables are built dynamically through routing protocols, and they update constantly as network topology changes. The problem is that routing tables can become temporarily inconsistent. When a link goes down or a route is withdrawn, some routers may still have stale entries pointing traffic toward a path that no longer leads to the destination. In these moments, a packet can get caught in a routing loop — bouncing between two or more routers that keep forwarding it back and forth, each one believing the other is closer to the destination.
Without any safeguard, a looping packet would never stop. It would consume processing power on every router it touches, eat into available bandwidth on every link it crosses, and multiply the problem when combined with other looping packets during the same convergence event. A single misconfigured route could cascade into serious congestion across an entire network segment.
TTL was designed specifically to solve this. By giving every packet a finite number of hops it can survive, the protocol guarantees that even a looping packet will eventually be destroyed. When the TTL hits zero at any router along the way, that router drops the packet and generates an ICMP Time Exceeded message (Type 11, Code 0) back to the original sender. This mechanism acts as a built-in safety net across the entire internet. It does not prevent routing loops from occurring — routing protocols handle convergence — but it ensures that the damage from a loop is always bounded. The packet dies after a fixed number of hops regardless of what the routing tables say.
This design decision, defined originally in RFC 791 (the IPv4 specification), remains one of the most fundamental protections in IP networking. Every router on the internet enforces it, and every operating system sets an initial TTL value precisely because this mechanism is non-negotiable.
How TTL Works Step by Step
The TTL mechanism operates at the IP layer — Layer 3 of the OSI model. It is handled entirely by the network stack of the sending device and by every router that processes the packet along the path. No application-level software needs to manage it. The process follows a strict sequence from the moment a packet is created to the moment it either reaches its destination or gets discarded.
How a Packet Gets Its TTL Value
When an operating system creates an IP packet, it writes a starting TTL value into the TTL field of the IPv4 header before the packet leaves the device. This value is determined by the OS kernel, not by the application generating the traffic. A Windows machine will typically stamp every outgoing packet with a TTL of 128. A Linux or macOS system will use 64. Some network equipment and older Unix systems default to 255.
The application — whether it is a browser, a ping utility, or a file transfer client — generally has no involvement in setting this value. However, advanced tools do allow manual override. For example, the ping command on most platforms accepts a flag to set a custom TTL:
ping -t 10 192.168.1.1 (Windows — but note: -i is used for TTL on Windows)
ping -t 10 192.168.1.1 (Linux/macOS uses -t for TTL)On Windows, the correct flag is -i to set the TTL value, while Linux and macOS use -t. Setting a low TTL manually is useful for diagnostic purposes, particularly when you want to control how far into the network a packet can travel — a technique that traceroute relies on heavily.
How TTL Decreases at Each Hop
Once the packet enters the network, every Layer 3 device — every router — that receives and forwards the packet must decrement the TTL value by exactly one before passing it along. This is not optional behavior. It is mandated by the IP specification. Switches operating purely at Layer 2 do not touch the TTL field because they forward frames based on MAC addresses without inspecting or modifying the IP header.
Here is a simplified example. A Linux machine sends a packet toward a server eight hops away. The packet starts with a TTL of 64. After the first router processes it, the TTL becomes 63. After the second, 62. By the time the packet reaches the destination server at hop eight, the TTL has been reduced to 56. The destination device reads the packet and does not decrement the TTL further — only forwarding routers do.
This decrement-by-one rule is what makes the TTL field function as a precise hop counter. The difference between the known starting TTL and the TTL value received at the destination tells you exactly how many routers the packet crossed.
What Happens When TTL Reaches Zero
If a router decrements the TTL and the result is zero, the router does not forward the packet. It drops the packet immediately and sends an ICMP Time Exceeded message back to the source IP address. This ICMP message has a type value of 11 and a code of 0, indicating “TTL expired in transit.”
The source device receives this ICMP reply and knows the packet never made it to its destination. Depending on the tool being used, this information is either displayed as an error — as in a failed ping — or used constructively, as in traceroute where TTL expiration is the core mechanism for mapping each hop along the route. The router that dropped the packet includes its own IP address in the ICMP response, which is how traceroute identifies intermediate devices.

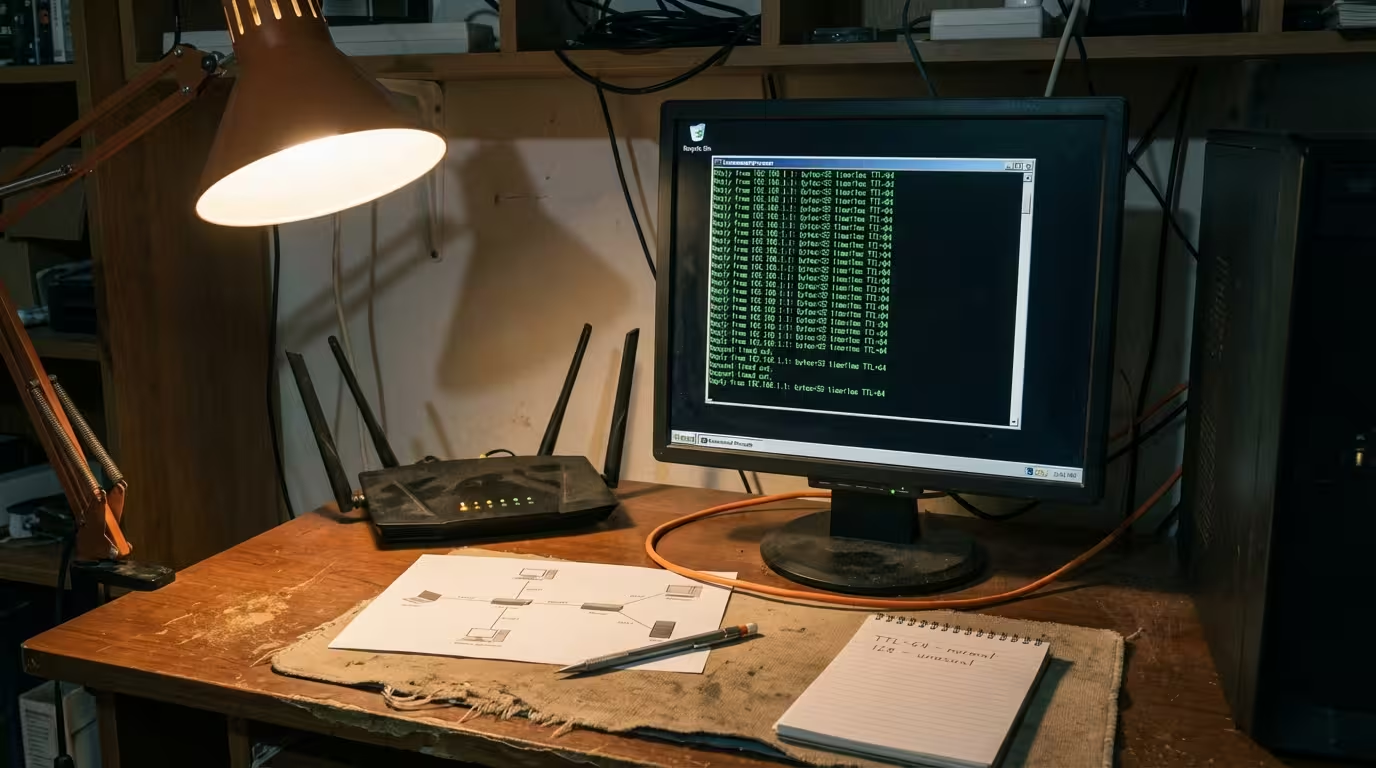
What Is TTL in Ping Results
When you run a ping command, the output includes several values for each reply — the response time in milliseconds, the size of the reply packet, and a TTL number. This TTL value is one of the most useful pieces of diagnostic information in the entire response, yet many users overlook it or do not understand what it represents. The TTL shown in a ping reply is not the TTL your machine set on the outgoing packet. It is the remaining TTL on the reply packet after it traveled back from the destination to your machine. Reading it correctly can tell you how many routers the response crossed and even hint at what operating system the remote device is running.
How to Read the TTL Number in a Ping Response
A standard ping response on Windows looks like this:
Reply from 8.8.8.8: bytes=32 time=14ms TTL=117On Linux or macOS, it appears slightly different but contains the same data:
64 bytes from 8.8.8.8: icmp_seq=1 ttl=117 time=14.2 msThe TTL=117 value in both outputs tells you how many hops the reply packet had left when it arrived at your machine. It does not tell you the starting TTL directly. It does not tell you the TTL of the packet you sent. It reflects only the return journey — the reply packet’s TTL after being decremented by every router between the remote server and your device.
This distinction matters. The packet you sent to 8.8.8.8 had its own TTL, set by your operating system. That packet’s TTL was decremented along the way to Google’s server. When Google’s server received your packet and generated a reply, it stamped a new TTL on the reply packet based on its own operating system defaults. That reply TTL then decreased with each hop on the way back to you.
Why the TTL You See Is Not the Starting TTL
The TTL displayed in your ping result has already been reduced by every router the reply passed through. If the remote server runs Linux and sets a starting TTL of 128, and the reply crosses 11 routers to reach you, the TTL you see will be 117. You are looking at the end result of the decrement process, not the beginning.
This is a common point of confusion. Many users assume a TTL of 117 means the remote device set its TTL to 117. That is almost never the case. Operating systems use round default values — 64, 128, or 255. A TTL of 117 in your ping result almost certainly started as 128 and was reduced by 11 hops along the return path.
How to Calculate How Many Hops a Packet Traveled
The calculation is straightforward once you know the common default TTL values. Take the received TTL, find the nearest default value above it, and subtract:
- TTL received: 117 → Nearest default above it: 128 → Hops = 128 − 117 = 11 hops
- TTL received: 52 → Nearest default above it: 64 → Hops = 64 − 52 = 12 hops
- TTL received: 241 → Nearest default above it: 255 → Hops = 255 − 241 = 14 hops
This method works reliably in the vast majority of cases. The only scenario where it can mislead is when a device has been configured with a non-standard starting TTL, but that is rare in practice. For everyday troubleshooting, rounding up to the nearest known default gives you an accurate hop count for the return path. Comparing this hop count across multiple ping tests to the same destination also helps you detect route changes — if the TTL suddenly shifts, the path through the network has changed.
Default TTL Values by Operating System
Different operating systems assign different default TTL values to outgoing packets. These defaults are set at the kernel level and apply to all IP traffic leaving the device unless a specific application overrides them. The most common defaults you will encounter are:
| Operating System | Default TTL |
|---|---|
| Linux | 64 |
| macOS | 64 |
| FreeBSD | 64 |
| Windows (7, 10, 11, Server) | 128 |
| Cisco IOS (routers/switches) | 255 |
| Solaris / AIX | 255 |
| Some IoT and embedded devices | 64 or 255 |
These values are not arbitrary. They represent deliberate choices by each operating system’s development team, and they have remained consistent across many versions.
Why Different Operating Systems Use Different TTL Values
The IP specification (RFC 791) recommends a default TTL that is large enough to ensure packets can reach any destination on the internet without expiring prematurely. It originally suggested 64 as a reasonable upper bound for the number of hops a packet would cross. At the time, internet topology was simpler and paths were shorter. A TTL of 64 was more than sufficient.
As networks grew more complex, Microsoft chose 128 for Windows — double the original recommendation — providing a wider margin for packets crossing deep or multi-layered enterprise networks. Cisco and some Unix-based systems went even further with 255, the maximum possible value in the 8-bit field, ensuring that packets from network infrastructure devices would essentially never expire due to hop count under normal conditions.
Linux and macOS have retained the original value of 64. In modern internet routing, most destinations are reachable within 15 to 20 hops, so 64 remains practical for general-purpose traffic. The choice of a lower default also offers a subtle security benefit — packets caught in a routing loop are destroyed faster, reducing the window of resource consumption.
How TTL Helps Identify the Remote Operating System
Because each operating system uses a predictable default TTL, the value you receive in a ping reply can serve as a basic OS fingerprinting tool. If you ping a server and receive a TTL of 117, you can calculate that the starting TTL was almost certainly 128, which points to a Windows machine. A TTL of 52 suggests a starting value of 64, indicating Linux, macOS, or FreeBSD. A TTL of 241 implies a starting value of 255, likely a Cisco device or a Unix-based system like Solaris.
This technique is not foolproof. Administrators can manually change the default TTL on any system. On Linux, for instance, the TTL can be modified with a single command:
sudo sysctl -w net.ipv4.ip_default_ttl=128This would make a Linux server appear to be a Windows machine based on TTL alone. Security-hardened environments sometimes do this deliberately to make OS fingerprinting less reliable. However, in most everyday troubleshooting scenarios, TTL-based OS identification is a quick and surprisingly accurate first guess.

Common TTL Values You Will See in Ping — What They Mean
When running ping tests across different targets, certain TTL values appear repeatedly. Understanding what each range typically indicates saves time during diagnosis:
- TTL 64 — The reply came from a device on the same local network (zero hops away) running Linux, macOS, or a similar system. The starting TTL was 64, and no routers decremented it.
- TTL 128 — A Windows device on the same local network, with no routers between you and the target.
- TTL 56–63 — Almost certainly a Linux or macOS device, with the packet having crossed 1 to 8 routers on the return path.
- TTL 112–127 — A Windows device, with the reply traversing 1 to 16 hops back to you.
- TTL 240–254 — A device using a starting TTL of 255 — typically network infrastructure like Cisco routers or legacy Unix systems — with the response crossing 1 to 15 hops.
- TTL 1 — The packet barely survived. It had only one hop left when it reached your machine, meaning either the path is extremely long or the starting TTL was set unusually low.
If you see a TTL value that does not fit neatly near 64, 128, or 255, consider the possibility that the remote device uses a custom TTL configuration. This is uncommon but does happen in hardened or non-standard environments. In most routine troubleshooting, though, the three standard defaults will explain virtually every TTL value you encounter in ping results.
What Is TTL Expired in Transit
If you have ever run a ping or traceroute and seen the message “TTL expired in transit,” you have witnessed the TTL mechanism doing exactly what it was designed to do — destroying a packet that exhausted its hop budget before reaching the destination. This message is not a generic timeout or connection failure. It is a specific ICMP error that tells you a router somewhere along the path decremented the TTL to zero and discarded the packet.
Why This Error Appears
The most common cause of a TTL expired error during a normal ping is a routing loop. When two or more routers have inconsistent routing tables, they can forward a packet back and forth between each other. Each pass through a router subtracts one from the TTL. Eventually, the TTL hits zero, the packet is dropped, and the router that dropped it sends the ICMP Time Exceeded message back to your machine. Your ping utility displays this as “TTL expired in transit.”
However, routing loops are not the only cause. This error also appears when:
- The starting TTL is too low. If you manually set a very low TTL — say 5 — and the destination is 12 hops away, the packet will expire before it arrives. This is not a network problem. It is expected behavior.
- The network path is unusually long. In rare cases involving satellite links, VPN tunnels, or heavily segmented enterprise networks, the hop count can be high enough that even a default TTL of 64 is not sufficient. This is uncommon on the public internet but can happen in complex private networks.
- A tunnel or VPN adds hidden hops. GRE tunnels, IPsec tunnels, and MPLS paths can each add hop decrements that are not visible in a standard traceroute. A packet may appear to cross 10 hops but actually passes through 20 or more when tunnel encapsulation is factored in.
What It Tells You About the Network Path
A single TTL expired message during a ping test is worth investigating but may not indicate a serious problem. Transient routing inconsistencies during convergence can cause a brief loop that resolves itself within seconds. If you see one or two TTL expired replies in a long ping sequence, the network likely experienced a momentary route flap.
Persistent TTL expired errors are more concerning. If every ping to a specific destination returns this error, there is almost certainly a stable routing loop or a path so long that the TTL cannot survive the journey. In this case, running a traceroute will help you pinpoint where the loop is occurring — you will see the same two or three routers repeating in the output as the TTL increments.
The source IP address inside the TTL expired ICMP message also provides valuable information. It tells you exactly which router dropped the packet, giving you a starting point for diagnosing the issue — whether that means contacting your ISP, checking your own router configurations, or identifying a misconfigured route in your network.
How TTL Is Used in Traceroute
Traceroute is built entirely on the TTL expiration mechanism. Rather than treating TTL expiry as an error, traceroute deliberately triggers it at every hop along the path to map the route between your device and a destination.
The process works by sending a sequence of packets with incrementally increasing TTL values. The first packet is sent with a TTL of 1. The first router that receives it decrements the TTL to zero, drops the packet, and sends back an ICMP Time Exceeded message. Traceroute records the IP address of that router — that is hop 1. The next packet is sent with a TTL of 2. It survives the first router but expires at the second, revealing hop 2. This continues, with the TTL increasing by one each round, until a packet finally reaches the destination with TTL still above zero. The destination responds with a normal reply instead of a Time Exceeded error, and traceroute knows the path is complete.
On Linux and macOS, the default traceroute command uses UDP packets. On Windows, tracert uses ICMP echo requests. Both rely on the same TTL manipulation principle. The command is straightforward:
traceroute 8.8.8.8 (Linux/macOS)
tracert 8.8.8.8 (Windows)Each line in the output represents one hop, showing the router’s IP address and the round-trip time for that probe. Asterisks (* * *) in the output indicate that a router did not respond — either because it is configured to suppress ICMP replies or because a firewall blocked the response. This does not necessarily mean the path is broken. Many routers silently forward traffic without responding to expired TTL probes for security reasons. The key diagnostic value of traceroute lies in identifying where latency spikes occur, where packet loss begins, or where a routing loop is cycling packets between the same devices.

TTL in DNS — A Different Use of the Same Concept
TTL in DNS has nothing to do with hop counts or routers. It borrows the same term — Time to Live — but applies it as a cache duration timer measured in seconds. When a DNS server responds to a query, each record in the response includes a TTL value that tells the requesting resolver how long it is allowed to cache that result before it must query again for a fresh answer.
For example, if you query the A record for a domain and receive a TTL of 3600, your local DNS resolver will store that IP address for 3600 seconds — one hour. During that window, any repeated lookups for the same domain will be answered from cache without contacting the authoritative DNS server again. Once the TTL expires, the resolver discards the cached entry and fetches a new one on the next request.
DNS administrators control these TTL values directly in their zone files. A low TTL like 60 seconds means changes propagate quickly because resolvers refresh frequently, but it also increases query load on the authoritative server. A high TTL like 86400 (one day) reduces query volume but means changes take longer to reach all users. Before planned DNS changes — such as a server migration — administrators often lower the TTL in advance so that the transition takes effect faster once the record is updated.
The conceptual link between IP TTL and DNS TTL is the idea of limiting lifespan. In IP networking, TTL limits how far a packet can travel. In DNS, TTL limits how long a cached record remains valid. Both prevent stale or unnecessary data from persisting indefinitely, but they operate in completely different contexts.
TTL in CDN Caching — Another Use of TTL
Content Delivery Networks also use TTL to control how long cached content remains valid on their edge servers. When a CDN like Cloudflare, Akamai, or AWS CloudFront caches a web page, image, or API response, the TTL determines when that cached copy expires and the edge server must fetch a fresh version from the origin server.
CDN TTL values are typically set through HTTP cache-control headers sent by the origin server. The Cache-Control: max-age=600 header, for instance, tells the CDN edge server to serve the cached version for 600 seconds before revalidating. Some CDN platforms also allow TTL overrides through their dashboard, giving operators control independent of the origin server’s headers.
The principle is identical to DNS TTL — it is a time-based expiration control. Short TTLs ensure users see updated content quickly but increase load on the origin server. Long TTLs improve performance and reduce origin traffic but risk serving stale content. Balancing this tradeoff is a routine part of CDN configuration. While the term TTL is the same across IP networking, DNS, and CDN caching, the underlying mechanics differ entirely. In networking discussions, always clarify which TTL you are referring to, as confusing them leads to miscommunication.
FAQ — Common Questions About TTL in Networking
What is TTL in networking?
TTL is a value in every IP packet header that limits the number of routers (hops) the packet can pass through. Each router decrements the TTL by one, and when it reaches zero, the packet is discarded.
What does TTL mean in ping results?
The TTL shown in a ping reply is the remaining hop count on the response packet after it traveled from the destination back to your machine. It reflects the return path, not the outgoing path.
Why does TTL decrease with each hop?
Every router that forwards a packet is required by the IP specification to subtract one from the TTL. This ensures packets cannot circulate indefinitely if a routing loop occurs.
How do I calculate how many hops a packet traveled using TTL?
Identify the nearest standard default above the received TTL (64, 128, or 255) and subtract. For example, a received TTL of 113 means 128 − 113 = 15 hops on the return path.
What is TTL expired in transit?
It is an ICMP error message generated when a router decrements a packet’s TTL to zero. The router drops the packet and notifies the sender that the packet could not reach its destination.
Can TTL tell me what operating system a remote device is running?
Yes, approximately. By calculating the starting TTL from the received value, you can infer the OS — 64 suggests Linux/macOS, 128 suggests Windows, and 255 suggests Cisco or legacy Unix.
What happens when TTL reaches zero?
The router that decremented the TTL to zero drops the packet immediately and sends an ICMP Time Exceeded (Type 11) message back to the source IP address.
How does traceroute use TTL to trace a network path?
Traceroute sends packets with incrementally increasing TTL values starting at 1. Each expired packet triggers an ICMP reply from the router that dropped it, revealing that hop’s IP address one at a time.
TTL is a straightforward but essential mechanism that protects every IP network from uncontrolled packet circulation. Whether you are reading ping results, running traceroute, analyzing DNS propagation, or tuning CDN cache behavior, understanding what TTL represents and how it behaves gives you a concrete diagnostic advantage. If you consistently see TTL expired errors when pinging a specific destination and traceroute confirms a routing loop or an unreachable path, the issue is almost certainly outside your local network — contact your ISP with the traceroute output so they can investigate the routing problem on their end. For local network TTL issues, check your own router configurations for circular static routes or misconfigured dynamic routing protocols. The TTL value never lies — it tells you exactly how many hops a packet survived, and that number is always the starting point for diagnosing what went wrong.